UX CONCEPTUAL PROJECT
Demystifying cyber security.
Making proactive measures simple for users.

The brief.
Identity Guard is an identity theft prevention service that offers insurance to their users. It’s in the best interest of both Identity Guard and their users to take every possible measure to protect their identity, their assets, and their privacy. However, monitoring sensitive information is only half the equation. Identity Guard needs to find a way to effectively encourage their users to take preventive measures like varied passwords, two-factor authentication, and weekly bank account reviews.
Duration.
2-week sprint
Team.
Me
Ellie Lampa
Bibi Tarin
Tools.
Figma
Whimsical
Method.
User surveys
User interviews
SME interviews
Affinity mapping
Wire-framing
Prototyping
Usability testing
THE PROBLEM
“No f---in’ clue.”
Overwhelmed and paralyzed by the unknown.
To our target user, cyber security seems dry, boring, complex, and esoteric. Furthermore, since it’s a preventative measure, they rarely think about it, which makes them effectively sitting ducks. Not only that, but when pressed about what cyber security actually is, they admit that they don’t really even know what it entails, or what they can do about it. They’ve simply never been taught.
Herein lies the problem: the target user is so overwhelmed by all the unknowns that they don’t know key information when going into the process. Information like: “Where do I begin? What measures do I need to take? How long will this all take? Where am I vulnerable? What information do I need on hand? What sites and apps do I have accounts with?” and most importantly “What questions am I NOT asking?”
Identity Guards current product fails to provide answers to these questions, thereby doing nothing to encourage users to take these steps.
THE SOLUTION
Spell it out.
Provide a clear roadmap to online security.
We believed that providing clear, easy-to-follow guidance would provide the user with enough knowledge and confidence to take the precautionary security measures.
This would come in the form of adding a password manager to the website and linking your bank account for easy review. We believed that adding an extra tab to the portal navigation for “best practices” with a clear step-by-step guide would provide them with a roadmap for success. Not only would we chart out the process in discrete steps, we would show their progress, provide time estimates, and show how vulnerable they are without them. Additionally, we believed that providing bite-sized pockets of information would be just enough to inform the user of what they were doing and why it is important.
Solution objective.
Simplify cyber security concepts and measures.
2. Lay out what needs to be done.
3. Provide a digestible roadmap.
How we approached it.
Discover why most people don’t take the necessary precautions.
In order to successfully deliver an impactful design solution, we had to figure out why users were neglecting to implement key security practices. Surveying and interviewing users gave us qualitative insights, straight from the users’ mouths, with the opportunity to explore motives and attitudes on the spot. These surveys and interviews revealed general attitudes and behaviors that helped us suss out the core issue at hand.
Getting the bigger picture.
Now that we had compiled a large amount of insights from the surveys and interviews, we had to parse out the trends. By performing affinity mapping, common trends started to appear that would help us create a solution that would address the actual problem.
Refining our initial iteration.
Once we had a working prototype based off of our previous findings, we performed usability tests to unveil our blindspots. The tests revealed a number of insights that we incorporated into our final prototype, making it stronger and even more intuitive.
Deliverables.
Remove the confusing dashboard altogether.
The initial dashboard that Identity Guard had on their portal was confusing, overwhelming, and redundant. We removed it all together, replacing it with “finish set-up” landing page to emphasize the importance of these steps.
Create an easy, digestible roadmap to security.
By adding a clear progress bar, and laying out discrete actionable tiles with time estimates and basic information, we simplified the thorough process of taking 100% precaution. No unknowns were left unexposed.
Provide accurate feedback.
Previously on the Identity Guard portal, there was a security score that failed to create a sense of urgency around key cyber security practices. In order to give users the impetus to perform these measures, we lowered the base security score, gave it a yellow “incomplete” color, and marked the individual as “vulnerable.” In addition, when the user completes a suggested security measure, they receive direct feedback as the score turns from a yellow low-number to a green high-number.
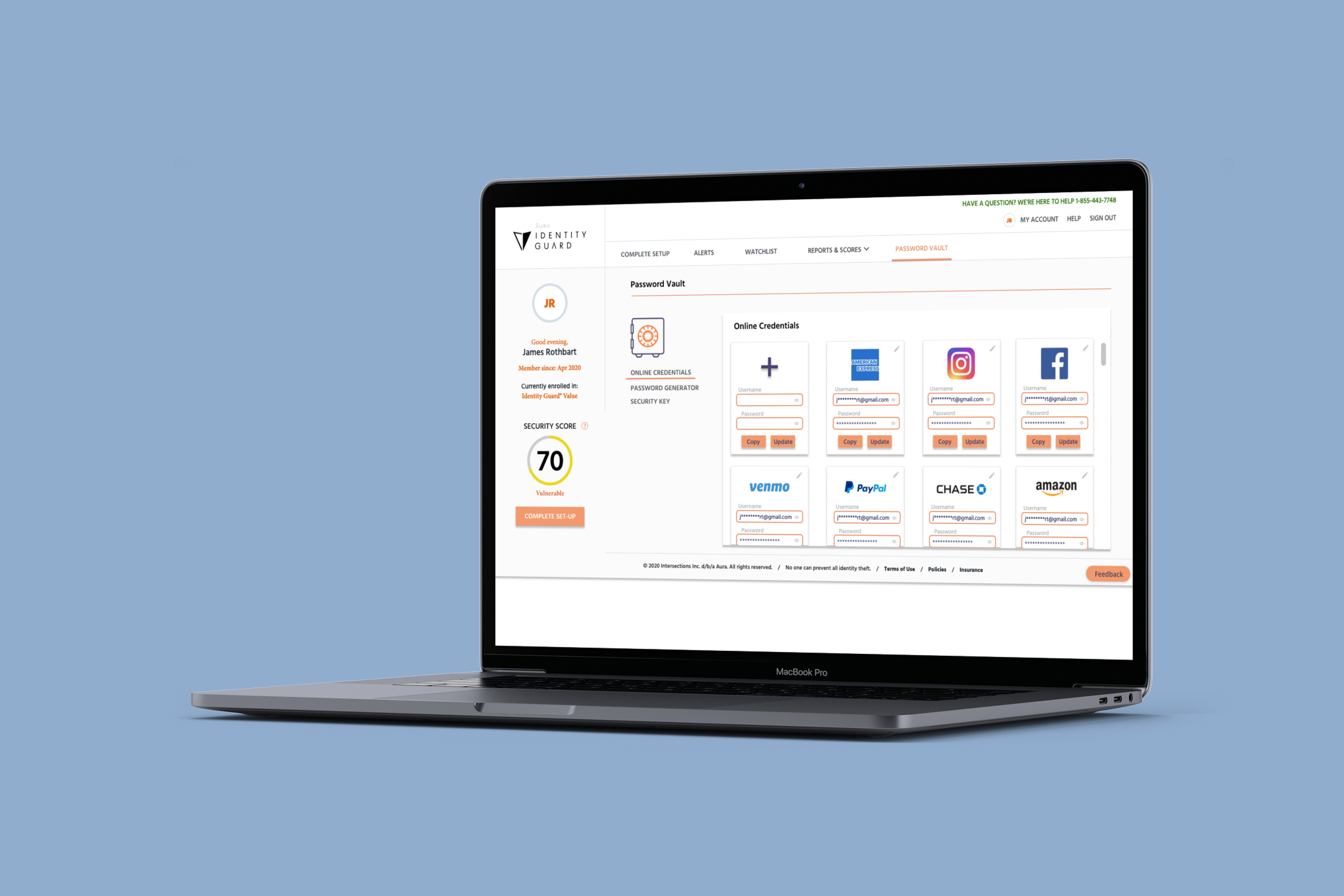
Built-in password manager.
In order to avoid directing users off the portal, we decided to bake in a password manager. By doing this, we were able to reduce the amount of effort and self-learning the user has to do, as well as reduce the time and distance the user has to go to complete this task. By making it simple and easy to use, the user is much more likely to understand what a password manager is, and incorporate it into their security arsenal.
Results and reflections.
Flesh out secondary security measures.
While two weeks was enough to flesh out the roadmap and password manager features, there are still two features that needed to be built: the security key and the bank account monitoring. For these features we need a way to easily purchase a security key directly from Identity Guard, as well as easy instructions on how to implement it. Additionally we need to incorporate a method of checking your bank statements via Identity Guard so that the user doesn’t have to bounce around multiple websites and logins.
Usability, usability, usability.
Even though our second iteration was quite strong and intuitive, there are still a number of features missing from the product, as listed above. Before sending out the design to engineering, we need to flesh out the rest of the features and perform usability tests on each feature. Then it is a matter of refining our design based on the insights we get from our usability tests. Once the product is thorough and smooth, it is ready to be built.
Get in touch.
Let’s build something together.
jamesrothbart[at]gmail[dot]com
Oakland, San Francisco Bay Area